Digital Library[ Search Result ]
Geographical Adaptive Attention Model for Points of Interest Recommendation
Muyeon Jo, Sejin Chun, Jungkyu Han
http://doi.org/10.5626/JOK.2025.52.3.217
Geographical influence, stemming from the location of Points of Interest (POIs), plays a vital role in POI recommendation. Most current studies utilize geographical information such as distance and location to define and extract POI-specific geographical influences for personalized recommendations. These approaches primarily emphasize distance-based influence, which gauges user preferences based on proximity, while often overlooking area-based influence, which reflects preferences for regions with specific POI characteristics. This paper introduces a POI recommendation model based on an attention network that integrates both distance- and area-based influences. The model adaptively assesses how previously visited POIs impact the likelihood of visiting a target POI, taking into account regional characteristics and user preferences. Experiments conducted on real-world datasets indicate that the proposed method significantly outperforms baseline models, achieving improvements of approximately 6–12% in Prec@10, 8–10% in Recall@10, and 6–7% in HR@10.
Efficient Ways of Attack for Network Isolation
Kyu Seok Han, Jiwon Yoon, Taekyu Kim, Young Woo Park, Jungkyu Han
http://doi.org/10.5626/JOK.2018.45.5.489
Many devices and objects have recently been connected to the network using the Internet of Thing technology. In a local area network (LAN) network for small scale, many devices are connected and the complexity of the network topology is greatly increased. Large-scale networks of such small-scale networks are also expanding nationwide. he flow of gathering and spreading data in a concentrated or distributed manner within a large network is being made. This is useful for various industries, financial, telecommunications, military, and power generation facilities in statebased industries use the nationwide Internet network to control and maintain a stream of data that can cope with emergency situations. In a network environment that has such a circumstance, if a critical device (node) or a small range of network (LAN) that is involved in the control, data collection, storage, or data processing is isolated and isolated from the entire network. This paper discusses techniques for isolating critical LANs or Nodes in large networks.
Search
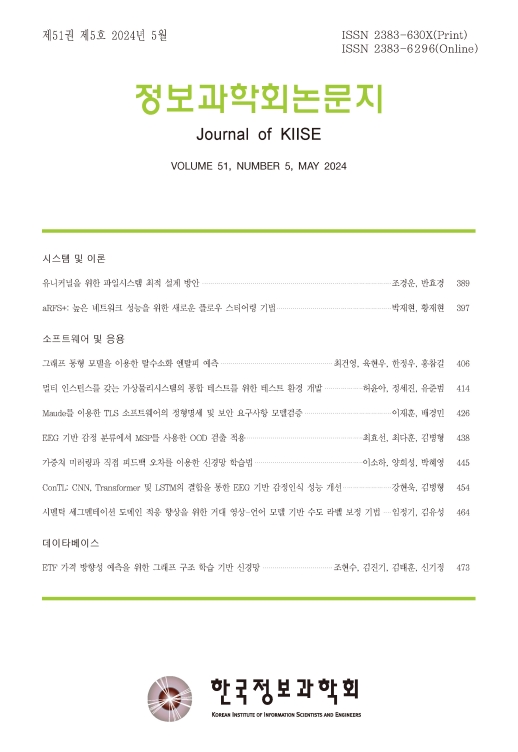
Journal of KIISE
- ISSN : 2383-630X(Print)
- ISSN : 2383-6296(Electronic)
- KCI Accredited Journal
Editorial Office
- Tel. +82-2-588-9240
- Fax. +82-2-521-1352
- E-mail. chwoo@kiise.or.kr
