Digital Library[ Search Result ]
Analyzing the Effects of API Calls in Android Malware Detection Using Machine Learning
Seonghyun Park, Munyeong Kang, Jihyeon Park, Seong-je Cho, Sangchul Han
http://doi.org/10.5626/JOK.2021.48.3.257
This paper evaluates the effect of preprocessing and representing API call information on the accuracy of the system to detect malicious Android apps. We extract API calls that access or control sensitive data from target apps, and use the calls in machine learning algorithms to detect malicious apps. We then determine which expression of the API calls is most effective in classifying the apps as malicious or benign. Four ways of representing each API call are considered: class/method name with and without arguments/return type, and its presence (whether an API is called or not) and its frequency if called. The detection system has performed slightly better when the arguments/return type and the frequency of each API call were considered together. Its feature size was most efficient when considering the class/method name and the presence of each API call.
An Effective Technique for Protecting Application Data using Security Enhanced (SE) Android in Rooted Android Phones
This paper analyzes security threats in Security Enhanced (SE) Android and proposes a new technique to efficiently protect application data including private information on rooted Android phones. On an unrooted device, application data can be accessed by the application itself according to the access control models. However, on a rooted device, a root-privileged shell can disable part or all of the access control model enforcement procedures. Therefore, a root-privileged shell can directly access sensitive data of other applications, and a malicious application can leak the data of other applications outside the device. To address this problem, the proposed technique allows only some specific processes to access to the data of other applications including private information by modifying the existing SEAndroid Linux Security Module (LSM) Hook function. Also, a new domain type of process is added to the target system to enforce stronger security rules. In addition, the proposed technique separates the directory type of a newly installed application and the directory type of previously installed applications. Experimental results show that the proposed technique can effectively protect the data of each application and incur performance overhead up to or less than 2 seconds.
Classifying Windows Executables using API-based Information and Machine Learning
DaeHee Cho, Kyeonghwan Lim, Seong-je Cho, Sangchul Han, Young-sup Hwang
Software classification has several applications such as copyright infringement detection, malware classification, and software automatic categorization in software repositories. It can be also employed by software filtering systems to prevent the transmission of illegal software. If illegal software is identified by measuring software similarity in software filtering systems, the average number of comparisons can be reduced by shrinking the search space. In this study, we focused on the classification of Windows executables using API call information and machine learning. We evaluated the classification performance of machine learning-based classifier according to the refinement method for API information and machine learning algorithm. The results showed that the classification success rate of SVM (Support Vector Machine) with PolyKernel was higher than other algorithms. Since the API call information can be extracted from binary executables and machine learning-based classifier can identify tampered executables, API call information and machine learning-based software classifiers are suitable for software filtering systems.
An Effective Technique for Detecting Vulnerabilities in Android Device Drivers
Android- and Linux-based embedded systems require device drivers, which are structured and built in kernel functions. However, device driver software (firmware) provided by various 3rd parties is not usually checked in terms of their security requirements but is simply included in the final products, that is, Android-based smart phones. In addition, static analysis, which is generally used to detect vulnerabilities, may result in extra cost to detect critical security issues such as privilege escalation due to its large proportion of false positive results. In this paper, we propose and evaluate an effective technique to detect vulnerabilities in Android device drivers using both static and dynamic analyses.
Detection of an Open-Source Software Module based on Function-level Features
As open-source software (OSS) becomes more widely used, many users breach the terms in the license agreement of OSS, or reuse a vulnerable OSS module. Therefore, a technique needs to be developed for investigating if a binary program includes an OSS module. In this paper, we propose an efficient technique to detect a particular OSS module in an executable program using its function-level features. The conventional methods are inappropriate for determining whether a module is contained in a specific program because they usually measure the similarity between whole programs. Our technique determines whether an executable program contains a certain OSS module by extracting features such as its function-level instructions, control flow graph, and the structural attributes of a function from both the program and the module, and comparing the similarity of features. In order to demonstrate the efficiency of the proposed technique, we evaluate it in terms of the size of features, detection accuracy, execution overhead, and resilience to compiler optimizations.
Search
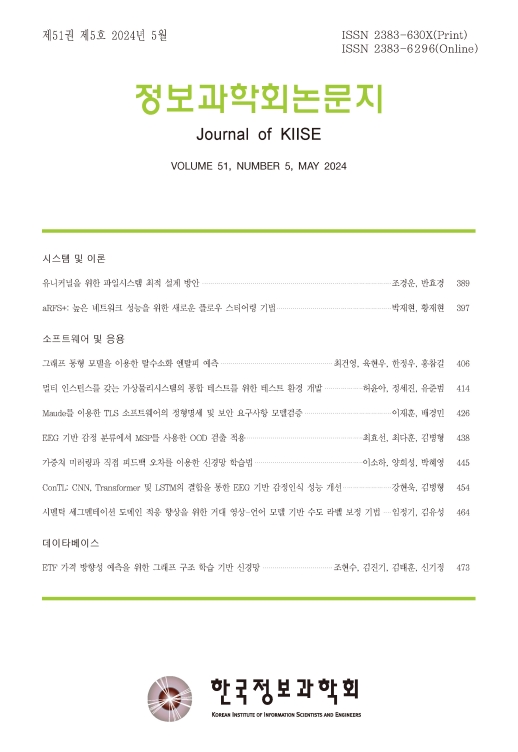
Journal of KIISE
- ISSN : 2383-630X(Print)
- ISSN : 2383-6296(Electronic)
- KCI Accredited Journal
Editorial Office
- Tel. +82-2-588-9240
- Fax. +82-2-521-1352
- E-mail. chwoo@kiise.or.kr
