Digital Library[ Search Result ]
Models for Privacy-preserving Data Publishing : A Survey
Jongseon Kim, Kijung Jung, Hyukki Lee, Soohyung Kim, Jong Wook Kim, Yon Dohn Chung
In recent years, data are actively exploited in various fields. Hence, there is a strong demand for sharing and publishing data. However, sensitive information regarding people can breach the privacy of an individual. To publish data while protecting an individual’s privacy with minimal information distortion, the privacy- preserving data publishing(PPDP) has been explored. PPDP assumes various attacker models and has been developed according to privacy models which are principles to protect against privacy breaching attacks. In this paper, we first present the concept of privacy breaching attacks. Subsequently, we classify the privacy models according to the privacy breaching attacks. We further clarify the differences and requirements of each privacy model.
Privacy-Preserving Self-Certified Public Auditing for Secure Cloud Storage
Mokryeon Baek, Dongmin Kim, Ik Rae Jeong
With a cloud storage service, data owners can easily access their outsourced data in cloud storage on different devices and at different locations, and can share their data with others. However, as the users no longer physically have possession of their outsourced data and the cloud still facing the existence of internal/external threats, the task of checking the data integrity is formidable. Over recent years, numerous schemes have been proposed to ensure data integrity in an untrusted cloud. However, the existing public auditing schemes use a third-party auditor(TPA) to execute high computation to check data integrity and may still face many security threats. In this paper, we first demonstrate that the scheme proposed by Zhang et al. is not secure against our two threat models, and then we propose a self-certified public auditing scheme to eliminate the security threats and guarantee a constant communication cost. Moreover, we prove the securities of our public auditing scheme under three security models.
Secure Multiparty Computation of Principal Component Analysis
Sang-Pil Kim, Sanghun Lee, Myeong-Seon Gil, Yang-Sae Moon, Hee-Sun Won
In recent years, many research efforts have been made on privacy-preserving data mining (PPDM) in data of large volume. In this paper, we propose a PPDM solution based on principal component analysis (PCA), which can be widely used in computing correlation among sensitive data sets. The general method of computing PCA is to collect all the data spread in multiple nodes into a single node before starting the PCA computation; however, this approach discloses sensitive data of individual nodes, involves a large amount of computation, and incurs large communication overheads. To solve the problem, in this paper, we present an efficient method that securely computes PCA without the need to collect all the data. The proposed method shares only limited information among individual nodes, but obtains the same result as that of the original PCA. In addition, we present a dimensionality reduction technique for the proposed method and use it to improve the performance of secure similar document detection. Finally, through various experiments, we show that the proposed method effectively and efficiently works in a large amount of multi-dimensional data.
A Spatial Transformation Scheme Supporting Data Privacy and Query Integrity for Outsourced Databases
Hyeong-Il Kim, Young-Ho Song, Jaewoo Chang
Due to the popularity of location-based services, the amount of generated spatial data in daily life has been dramatically increasing. Therefore, spatial database outsourcing has become popular for data owners to reduce the spatial database management cost. The most important consideration in database outsourcing is meeting the privacy requirements and guarantying the integrity of the query result. However, most of existing database transformation techniques do not support both of the data privacy and integrity of the query result. To solve this problem, we propose a spatial data transformation scheme that utilizes the shearing transformation with rotation shifting. In addition, we described the attack models to measure the data privacy of database transformation schemes. Finally, we demonstrated through the experimental evaluations that our scheme provides high level of data protection against different kinds of attack models, compared to the existing schemes, while guaranteeing the integrity of the query result sets.
Exploiting Friend’s Username to De-anonymize Users across Heterogeneous Social Networking Sites
Nowadays, social networking sites (SNSs), such as Twitter, LinkedIn, and Tumblr, are coming into the forefront, due to the growth in the number of users. While users voluntarily provide their information in SNSs, privacy leakages resulting from the use of SNSs is becoming a problem owing to the evolution of large data processing techniques and the raising awareness of privacy. In order to solve this problem, the studies on protecting privacy on SNSs, based on graph and machine learning, have been conducted. However, examples of privacy leakages resulting from the advent of a new SNS are consistently being uncovered. In this paper, we propose a technique enabling a user to detect privacy leakages beforehand in the case where the service provider or third-party application developer threatens the SNS user’s privacy maliciously.
Secure Multi-Party Computation of Correlation Coefficients
Sun Kyong Hong, Sang Pil Kim, Hyo Sang Lim, Yang Sae Moon
In this paper, we address the problem of computing Pearson correlation coefficients and Spearman’s rank correlation coefficients in a secure manner while data providers preserve privacy of their own data in distributed environment. For a data mining or data analysis in the distributed environment, data providers(data owners) need to share their original data with each other. However, the original data may often contain very sensitive information, and thus, data providers do not prefer to disclose their original data for preserving privacy. In this paper, we formally define the secure correlation computation, SCC in short, as the problem of computing correlation coefficients in the distributed computing environment while preserving the data privacy (i.e., not disclosing the sensitive data) of multiple data providers. We then present SCC solutions for Pearson and Spearman’s correlation coefficients using secure scalar product. We show the correctness and secure property of the proposed solutions by presenting theorems and proving them formally. We also empirically show that the proposed solutions can be used for practical applications in the performance aspect.
Security Enhanced Authentication Protocol in LTE With Preserving User Location Privacy
Changhee Hahn, Hyunsoo Kwon, Junbeom Hur
The number of subscribers in 4th generation mobile system has been increased rapidly. Along with that, preserving subscribers’ privacy has become a hot issue. To prevent users’ location from being revealed publicly is important more than ever. In this paper, we first show that the privacy-related problem exists in user authentication procedure in 4th generation mobile system, especially LTE. Then, we suggest an attack model which allows an adversary to trace a user, i.e. he has an ability to determine whether the user is in his observation area. Such collecting subscribers’ location by an unauthorized third party may yield severe privacy problem. To keep users’ privacy intact, we propose a modified authentication protocol in LTE. Our scheme has low computational overhead and strong secrecy so that both the security and efficiency are achieved. Finally, we prove that our scheme is secure by using the automatic verification tool ProVerif.
Search
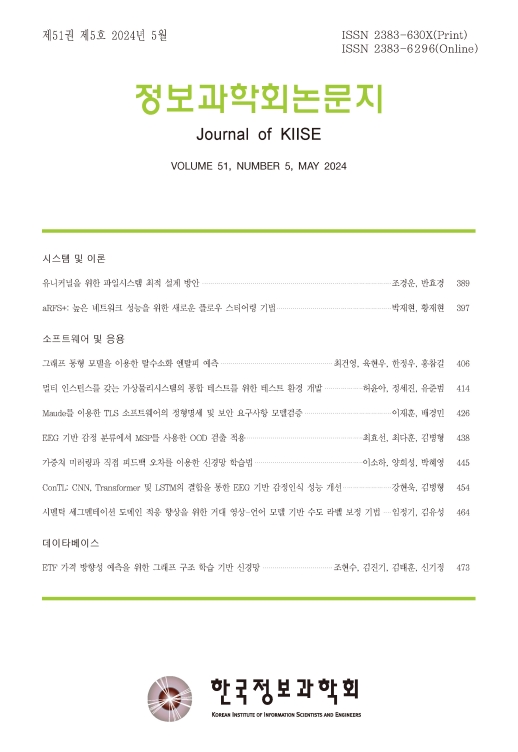
Journal of KIISE
- ISSN : 2383-630X(Print)
- ISSN : 2383-6296(Electronic)
- KCI Accredited Journal
Editorial Office
- Tel. +82-2-588-9240
- Fax. +82-2-521-1352
- E-mail. chwoo@kiise.or.kr
